Configuring Oracle OIF for Salesforce.com SAML SSO
Here is a quick how-to on configuring Oracle Identity Federation (OIF) as the SAML Identity Provider for Salesforce.com.
This turns out to be surprisingly easy to set up. For pre-requisites you should have the following in place:
- It is easiest if your OIF instance is configured to use POST SAML bindings by default. You can override this on a provider basis but most often you will use POST, so it makes sense to set it as the default.
- You need a salesforce.com account. Developer accounts are free and support SAML.
- Create a user in your ldap for testing SAML SSO. We will match on the users "mail" attribute. Set this to a relevant value (testuser@example.com). The mail attribute does not need to match the salesforce.com account id.
- This example assumes we are using OAM as the authentication engine for OIF, and they both are referencing the same ldap server.
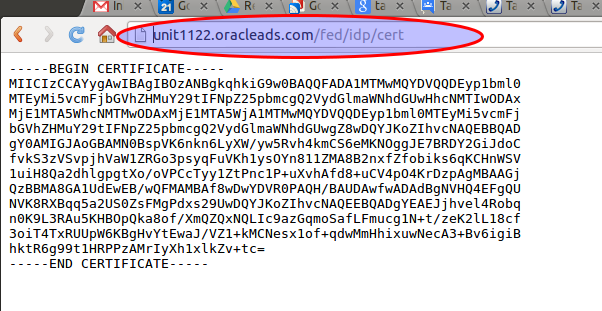
Step 1 is to import your OIF IdP cert into salesforce.com. The cert is available at http://example.com/fed/idp/cert (where example.com is replaced by your install domain /port). For example:
Save this cert to a text file, and import it into salesforce.com. The salesforce SAML SSO setup is under the Security Controls left hand nav bar:
On the salesforce SSO setting page perform the following:
- Import the saved certificate file.
- Set the issuer to the provider id for OIF. This is available from the OIF console under "Identity Provider" properties. It usually of the form: http://yourserver:7499/fed/idp. Note that the provider id must be a url format - but the id itself is opaque. In my example OIF is actually not available on port 7499 - but that's OK. The provider id is just for matching purposes.
- Check the SAML id user type and location as shown above
- Enter "mail" as the attribute name
After saving your changes, export the salesforce.com metadata and save it to a file.
At this time you should also set the salesforce.com Federation Id for your test user to match your ldap user email attribute. This is under the salesforce.com menu:
- Personal Setup -> My Personal Information -> Personal Information -> Edit.
You want to set the Federation Id under Single Sign On Information:
On your OIF console, navigate to Admin -> Federations and import the saved meta data:
If your defaults in OIF are correct, you are most likely "done". Test SSO out by going to the following url:
http://yourserver.com/fed/idp/initiatesso?providerid=https://saml.salesforce.com
Pro tip: The Firefox SAML tracer plugin lets you view what is being sent in the assertion.
If federation is not working the most likely cause is that the federation id does not match, or OIF is not sending the right attribute.
You can edit the salesforce.com provider settings in OIF to fiddle with this. For example:
You can also add an explicit attribute mapping (hit the "Edit" button above to add a mapping)
With my OIF defaults it "just worked". YMMV